MotoSim EG-VRC
High-Precision Robot Simulator (For Windows 7/10)
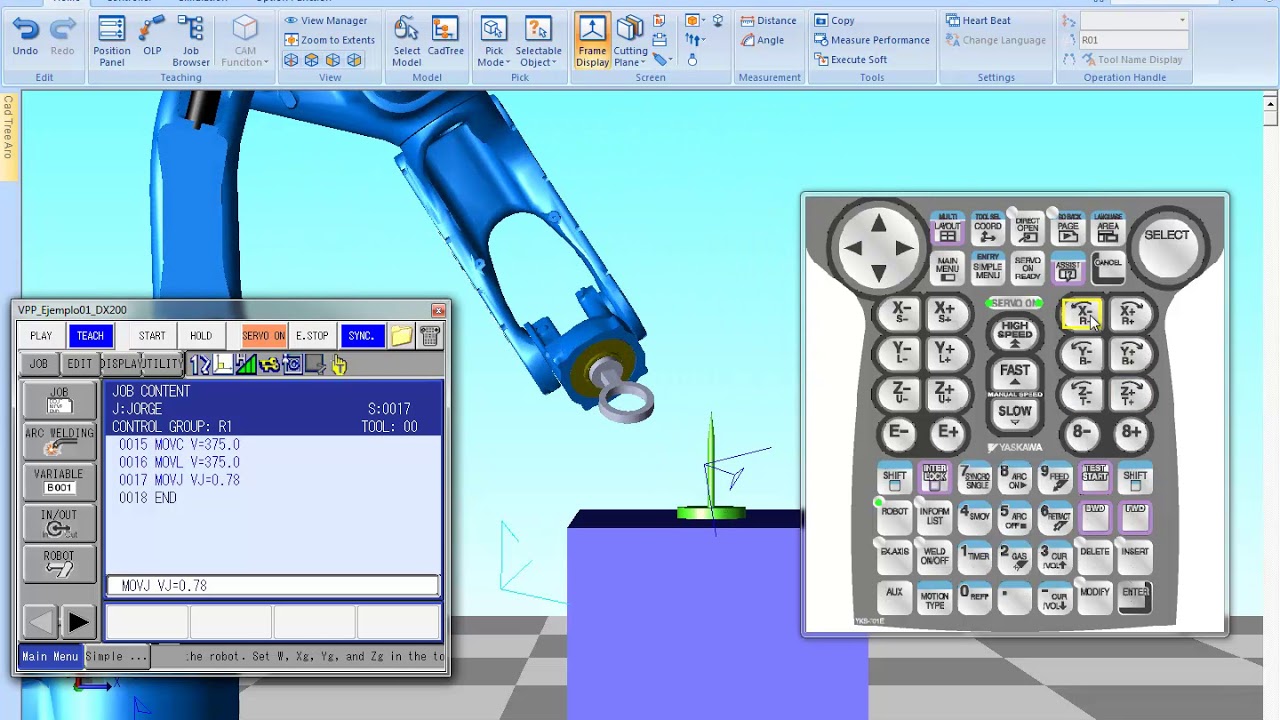
The robot simulator MotoSim EG-VRC can intuitively and quickly carry out operations, from supporting the construction of a robot system to its operation, using various functions. The CAM function imports native data directly from representative CAD software, which dramatically saves working time in comparison with the use of intermediate data, such as STEP and IGES. The visual path editor function visually checks job details and freely edits and teaches jobs. The JobPad can set characters, background colors, and fonts for job commands and perform batch grammar checks and auto complete, enabling users to edit jobs like writing by hand on a notepad. The MotoSim EG-VRC provides you with a wiser and smarter engineering environment.
Vision Function
- Equipped with the Virtual Robot Controller (VRC) function that has functions identical to that of an actual robot controller and the Virtual Programming Pendant (VPP) function.
- Has robot data compatibility that can be offered only by the developer of MOTOMAN as well as the online functions that enable automatic construction of VRC, monitoring, and file transfer through the linkage with an actual controller.
- Can quickly layout and create jobs using 3D-CAD data that supports various formats.
- The CAM function supporting various applications allows even entry-level robot users to easily and quickly layout and create jobs (CadPack ).
- The VRC technology enables highly accurate verification of cycle time.
- Supports the latest MOTOMAN models in all applications.